Access control systems help to manage entry into specific business areas. Many businesses use their access control system in conjunction with their intercom system at a reception desk to keep unwanted visitors from the office. ABF Security also has many customers who protect their IT rooms, files, and other high-value items. You can program the systems to unlock during certain times of the day or only allow cards to work during certain business hours. The possibilities are endless, and ABF Security is here to help you achieve the level of security that best suits your business!
In addition to offering security, access control systems allow you to monitor events in and around the office when you are not there. From a practical standpoint, it makes it easier to ensure that individuals are in the office when they should be while also allowing you to restrict access by location and monitor the activities of individuals and the systems in your office. Access control promotes efficiency, improves security, saves energy, and could even provide insurance discounts.
Property Management Made Easy
Conventional access limitation consists of keying doors differently and distributing the right keys to the right people, and even more primitive Do Not Enter signs stuck to a door. Are you sure taped signs will ensure your restricted areas are respected?
In some cases, limiting access may be about more than just keeping people out of an area but also keeping your personnel safe from unwelcome guests. So, how can you keep your employees safe? Access control is the most sensible option and can benefit systems of all sizes. Private information will remain that way and unauthorized visitors will not be able to enter the area. Your employees won’t have to carry a full ring of keys but will remain protected.
Lock, Limit, and Secure
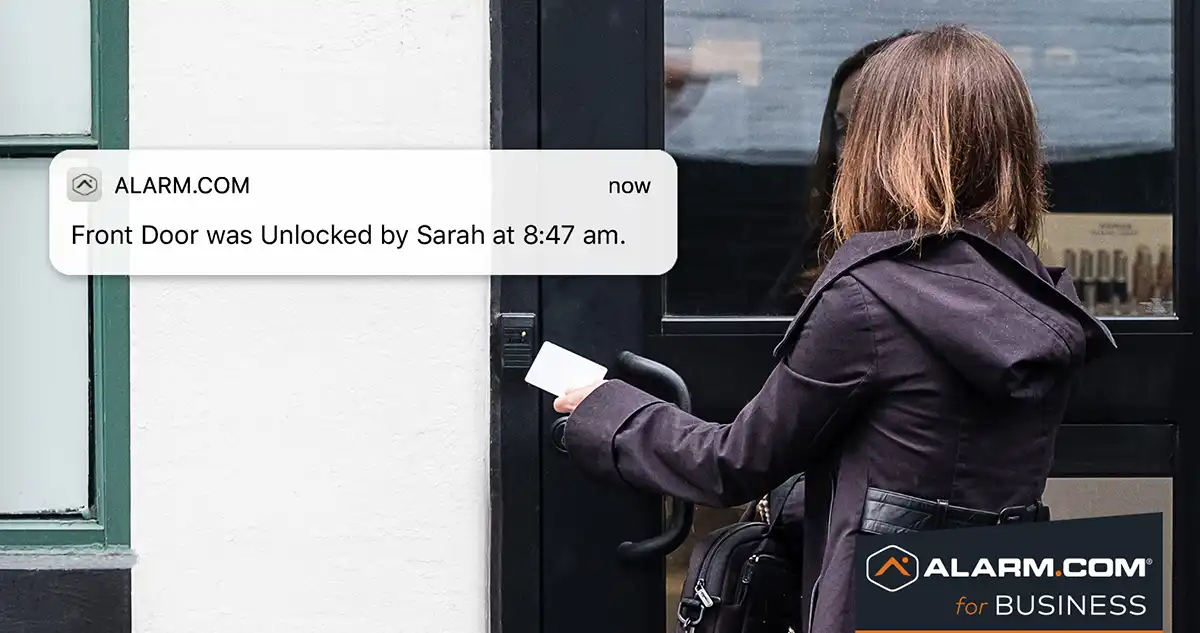
ABF Security’s commercial access control packages are custom-designed to fit your needs and application, regardless of how big or small. We have the solution for a single door to thousands of access points. With an access control system, you can accommodate almost any conceivable situation; each lock can have different access levels and privileges to restrict access by person, day, time, and event. Our partner, Alarm.com, offers cloud-based management with 24/7 monitoring, object detection, and real-time alerts.
Types of Access Control
There are four primary types of access control functionality, each based on the level of security you want for your organization.
Mandatory Access Control (MAC) limits access to resources based on the sensitivity of the information and the authorization of the user. Users can access only the information in an area to which their security labels entitle them. If the user’s security label does not have enough authority, the user cannot access the information.
Role-Based Access Control (RBAC) creates easy programming and adaptation to personnel changes. Access is not based so much on who a person is but on what group or classification the individual may have. For example, some areas are available to only your Sales personnel. An individual assigned to that group will gain access to all areas that particular group is allowed. If a person is promoted or moves to another group, the group assignment is the only thing to be changed.
Rule-Based Access Control (RuBAC) is similar to the RBAC by allowing or denying access to users based on limitations or rules defined by the owner. Rule-based access relies on many other circumstances, such as days of the week, time of day, emergency criteria, single-use access, or access for a specific time or event.
Discretionary Access Control (DAC) is the least restrictive by setting the factor that the user has a code or card for access. There is no additional questioning or confirmation, simply that the code or card allows entry, regardless of who is presenting the information. This type works well when the level of access control is locking an area and keeps from having to distribute keys to everyone with access.

How it Works
A commercial access control system works only when the door controller determines if it should grant access based on the credentials provided. A user presents their credentials to the reader, which could look very different based on the kind of commercial access control system. Then, the reader accepts the encrypted data and transfers it to the door controller. Once the door controller receives the data, it analyzes it to determine if the credentials provided are authorized to access the specified areas. If the authorization passes, the door controller notifies the door lock to release. Finally, the user may open the door to access the space.
Adding an access control system to your business is an investment that will provide you with an extensive ROI. Being able to control your property and important documents is enough reason to build a business case. Your access control system can also work alongside other security measures you might have, such as security cameras, alarm systems, and even cybersecurity measures. Centralizing these systems creates a holistic approach to protecting your property and assets. Our team is eager to help you connect your systems and regain control. Contact ABF Security today to protect your assets!

